Attackers can force Echos to hack themselves with self-issued commands

Popular “smart” device follows commands issued by its own speaker. What could go wrong?

Best Home Security Systems That Work with Alexa in 2024

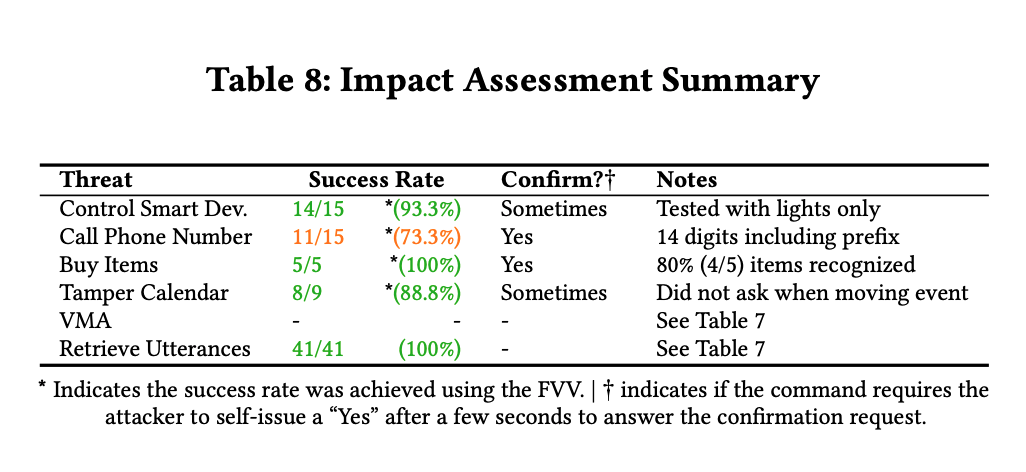
A survey on security analysis of echo devices - ScienceDirect
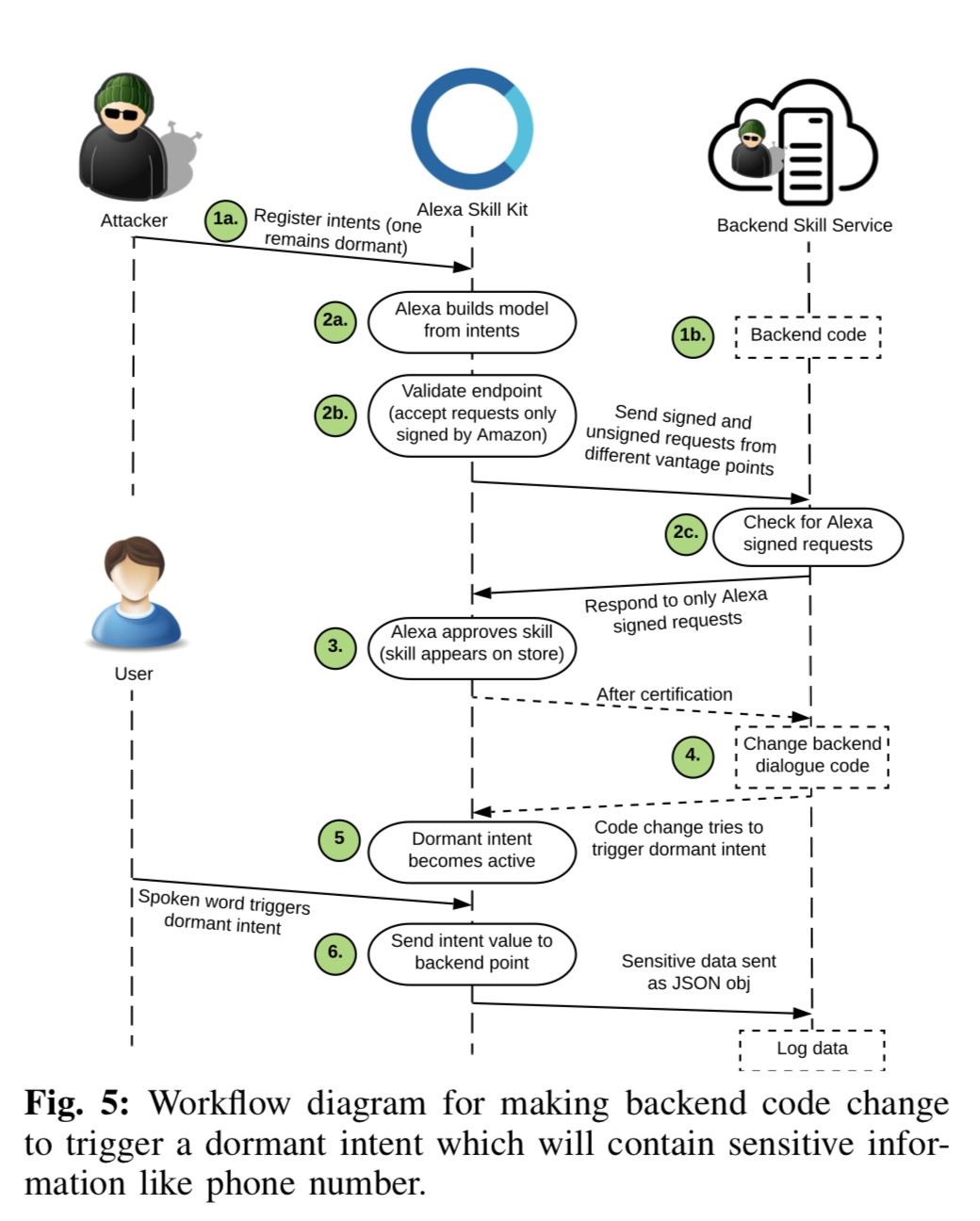
Mapping vulnerabilities in echo using alexa skills
The Mirai Confessions: Three Young Hackers Who Built a Web-Killing Monster Finally Tell Their Story
Attackers can force Echos to hack themselves with self-issued commands

How to Prevent SQL Injection: Attacks and Defense Techniques - Tutorial and Best Practices

s Echo smart speakers can be hacked to issue self-commands – The Cybersecurity Daily News

Echos Hack Themselves, Fraud Is Flourishing on Zelle, Samsung Galaxy Source Code Stolen - Shared Security Podcast

Denial-of-service attack - Wikipedia

What to Do When You've Been Hacked

A survey on security analysis of echo devices - ScienceDirect
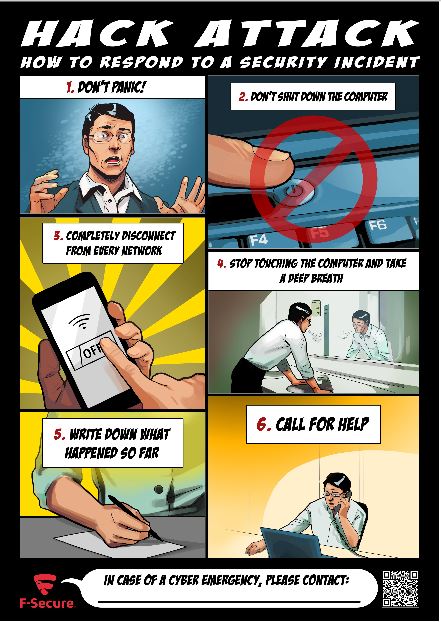
What you actually need to do if you're hacked - F-Secure Blog

The inside story of the world's most dangerous malware - E&E News by POLITICO