Vulnerable perimeter devices: a huge attack surface

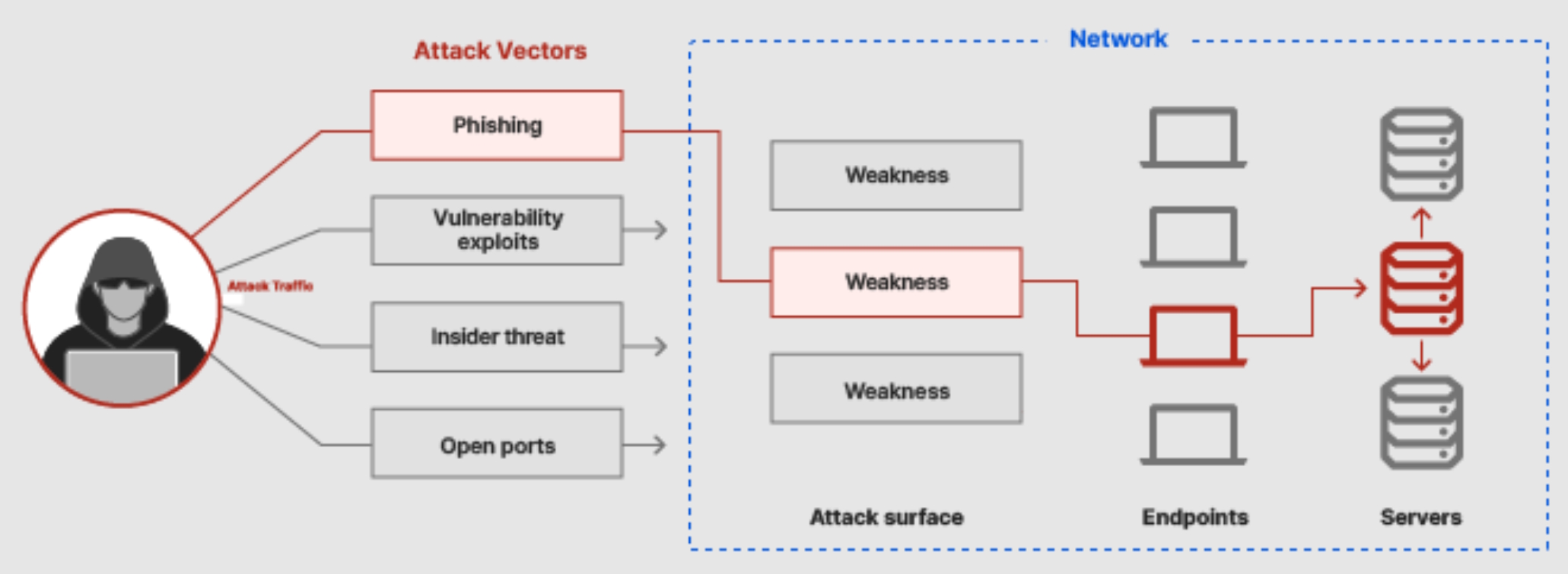
With the increase of critical gateway devices deployed to support off-premise work, companies across the world have to adapt to a new threat landscape where perimeter and remote access devices are now in the first line.
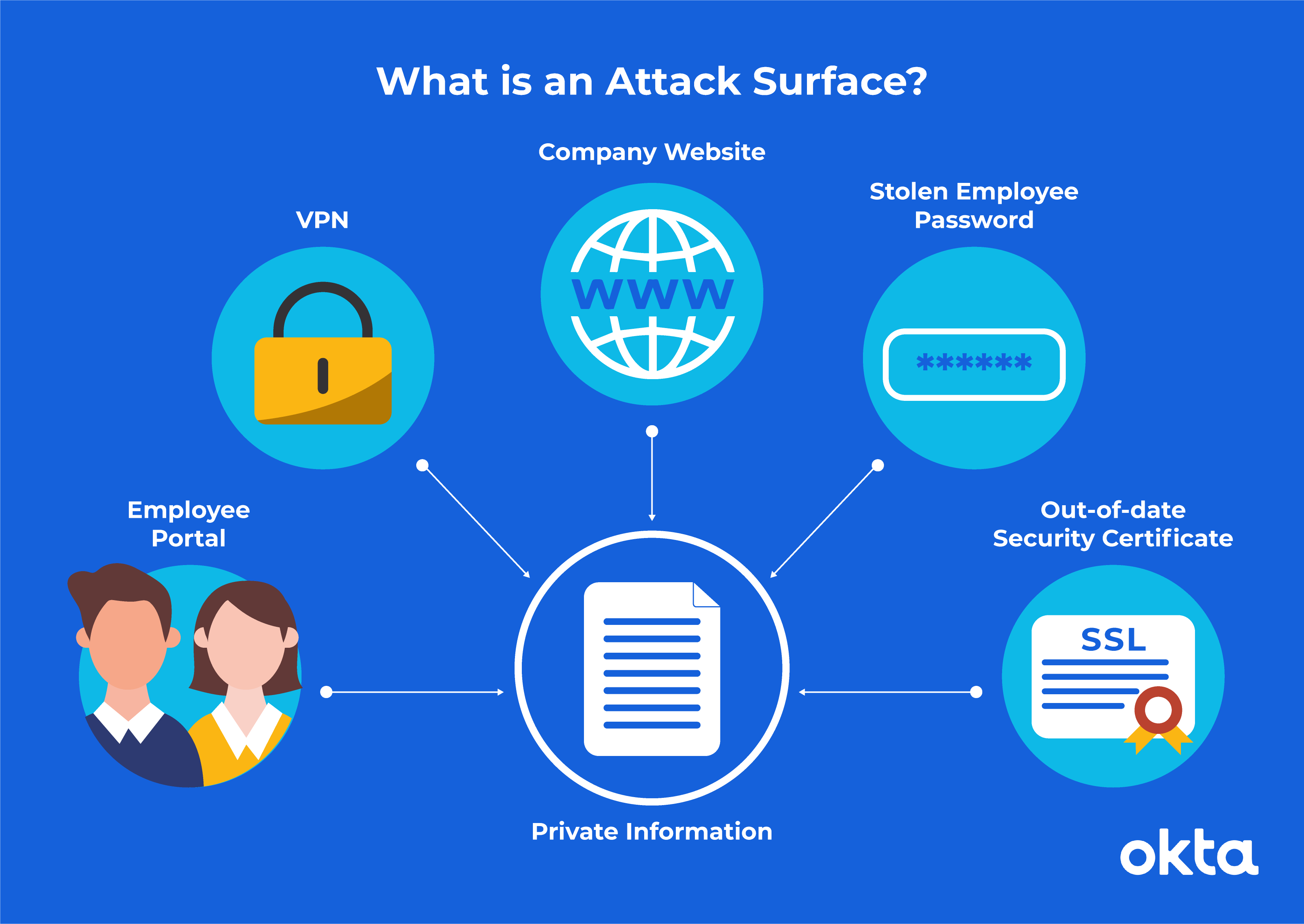
What is an Attack Surface? (And How to Reduce It)
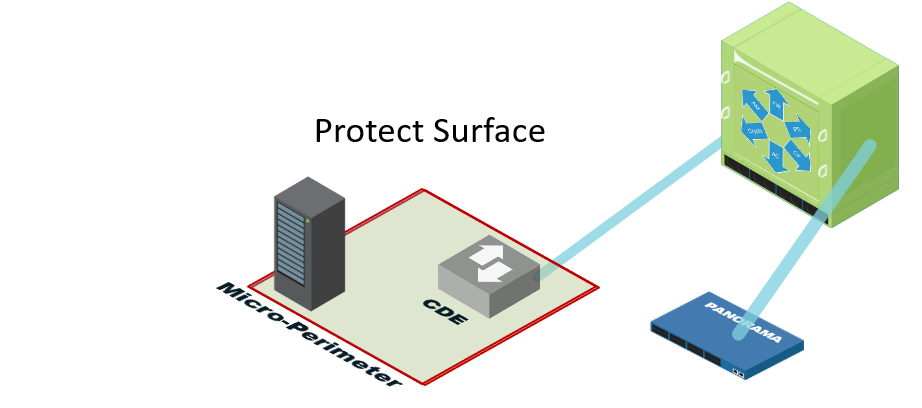
Define a Protect Surface to Massively Reduce Your Attack Surface
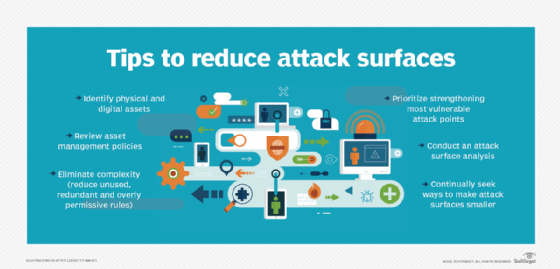
What is an attack surface? Definition from TechTarget

5 Ways to Reduce Your Attack Surface, 2018-08-02

Vulnerable perimeter devices: a huge attack surface
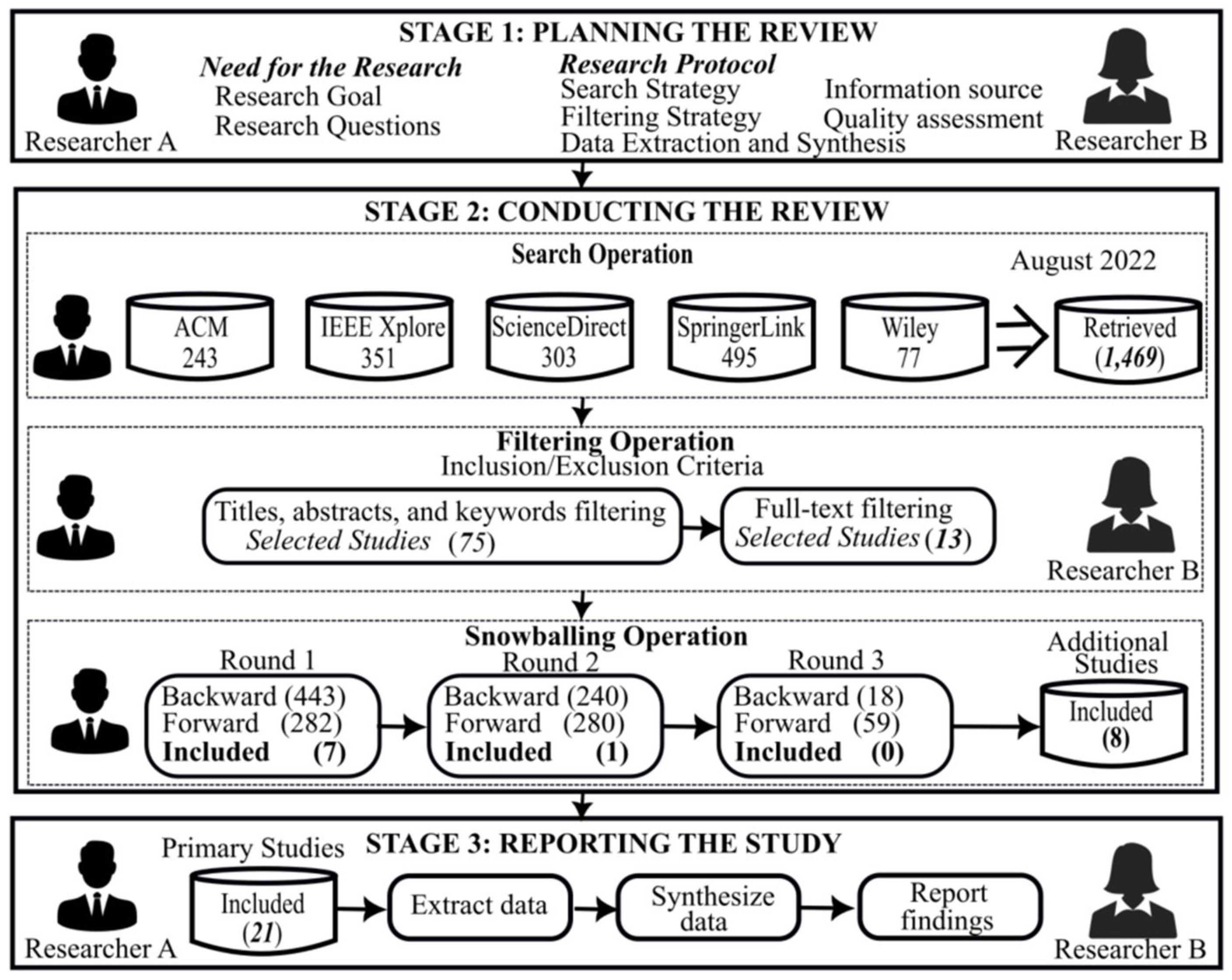
Computers, Free Full-Text

2020 Archives - Page 8 of 16 - Version 2 Limited

How To Protect Your Digital Perimeter

Top 10 Vulnerability Management Tools - Spiceworks

Products on your perimeter considered harmful (until

SCADAfence Archives - Page 9 of 10 - Version 2 Limited

[New feature] Discover your Network's Attack Surface
What is an Attack Surface? (And the Best Way to Reduce It)
How can we protect against IoT attacks?