Sizing Up Post-Quantum Signatures
How much room does TLS have for the big post-quantum signatures? We had a look: it’s tight.

Post-Quantum Adversarial Modeling: A User's Perspective

Deep dive into a post-quantum signature scheme

Making existing software quantum safe: A case study on IBM Db2

Cryptographic Competitions
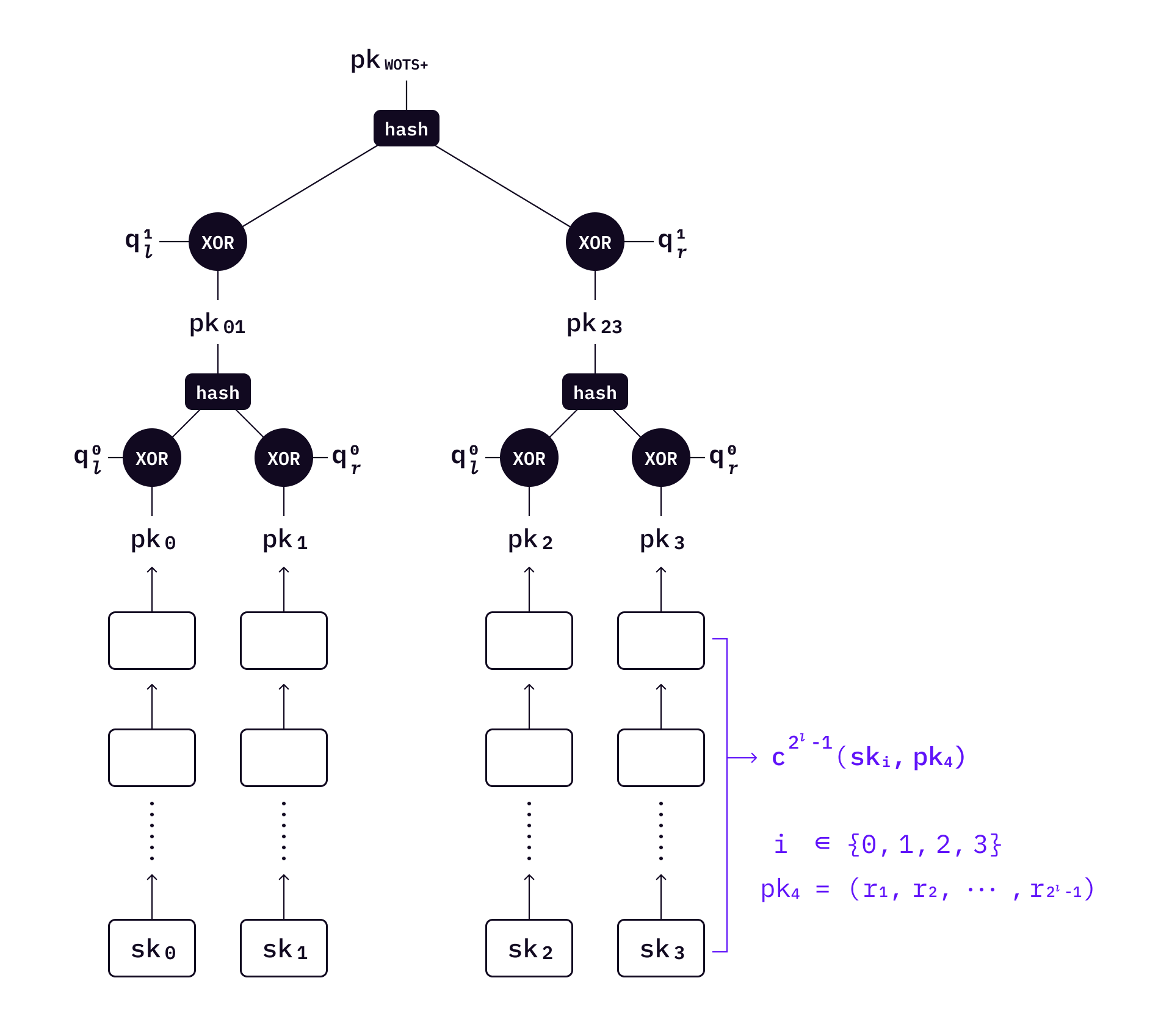
How do hash-based post-quantum digital signatures work? (Part 1
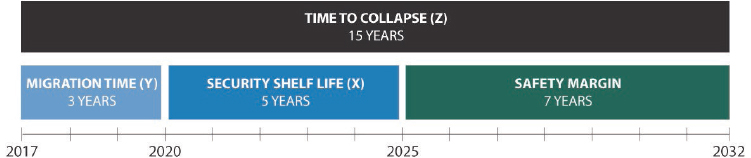
4 Quantum Computing's Implications for Cryptography
KEMTLS vs. Post-quantum TLS: Performance on Embedded Systems

Jared Crawford on LinkedIn: 🍿 My adventure continues with the

Shorter Hash-and-Sign Lattice-Based Signatures
Post-quantum cryptography: Hash-based signatures
A cryptographic canary against quantum computers · Siyu Chen, Eric

Post-Quantum Cryptography: Are We Ready for Q Day?

Lattice-based Signatures
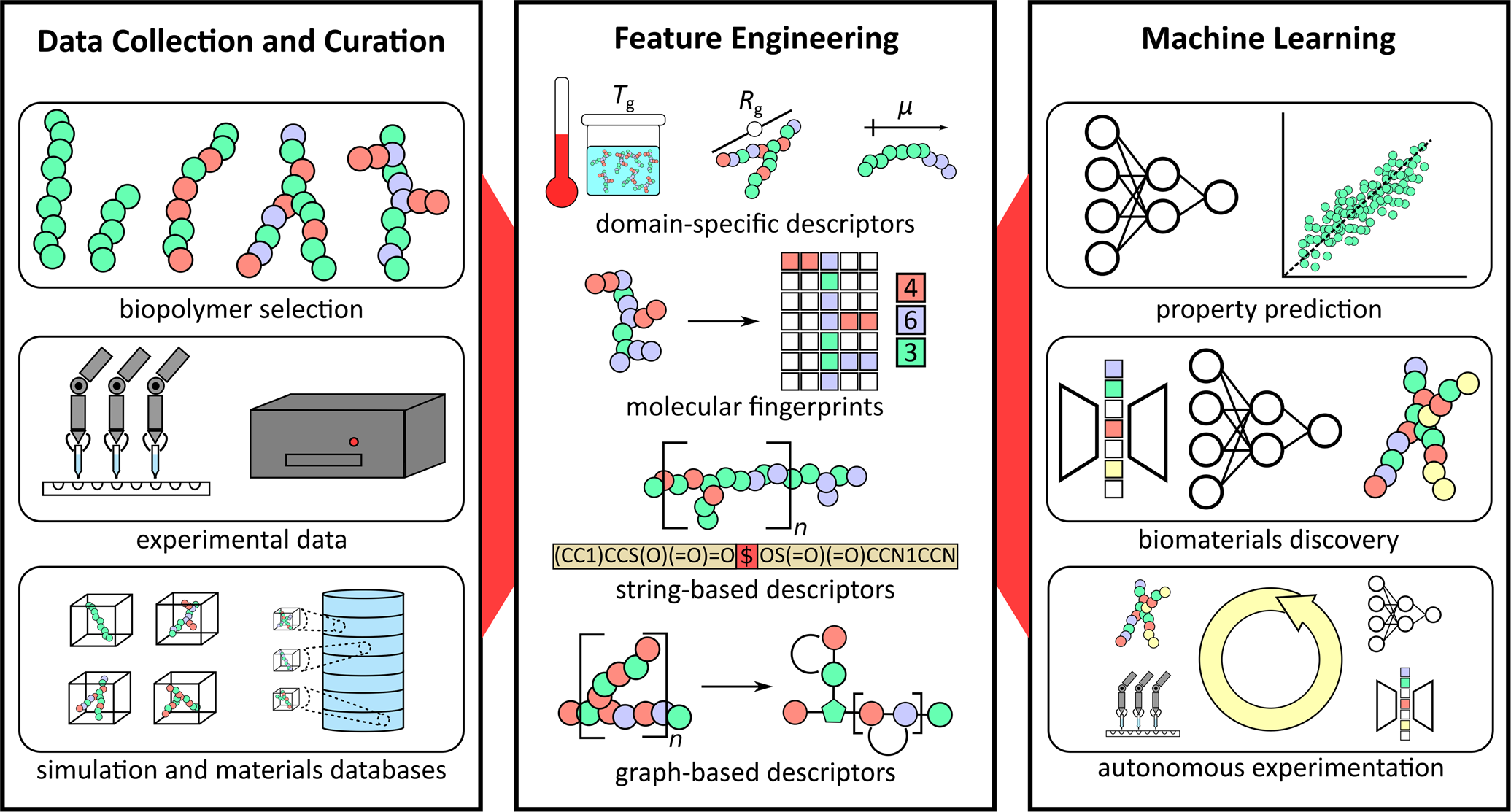
Sizing up feature descriptors for macromolecular machine learning