Dark endpoints: an invisible threat to your IT team

Invisible devices create significant blind spots that can leave IT departments helpless to act against a breach until it is already too late. A new report from Absolute found 13% of enterprise devices aren't connected to the corporate domain.
The Absolute platform delivers self-healing endpoint security and always-connected IT asset management to protect devices, data, applications and users — on and off the network.
Unmasking the Invisible Threat: Your Guide to Network Security

EPP vs. EDR: Why You Need Both - CrowdStrike

Endpoint Security Risks in your Organization and how to overcome
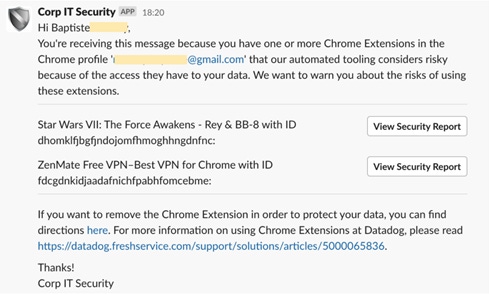
Malware Exploits Security Teams' Greatest Weakness: Poor Relationships With Employees

ThreatKey - You Won't Believe These 7 Shocking SaaS Security

The Internet of Things: Risks & Mitigation Strategies

The Driz Group - Cyber Security - The Driz Group Official Blog

How Lean Security Teams Can Overcome the Cybersecurity Spending

What Is Endpoint Detection and Response?- Spiceworks - Spiceworks

Thwarting an invisible threat: How AI sniffs out the Ursnif trojan

Security Teams Struggle to Get Started With Zero Trust

As firmware-level threats continue to gain popularity in the wild

Deconstructed Podcast: How the U.S. Makes Its Wars Invisible

Failed Fix? Endpoint Tools Overwhelmed, Underequipped to Handle